Many U.S.-based traders treat an exchange login as a routine IT action: enter credentials, 2FA, trade. That framing misses how account verification, custody choices, and the Web3 surface change your risk calculus. Using OKX is not just about gaining access to markets; it’s about managing layered attack surfaces (CEX account, Web3 wallet, biometric device), regulatory touchpoints (KYC), and operational trade-offs between convenience and control. This article walks through a concrete case — a U.S. derivatives trader re-establishing access after a locked device and a delisted alt token position — to show what happens under the hood, where things break, and practical rules that reduce friction and prevent permanent losses.
The case: Sarah, a professional options trader who keeps margin strategies on OKX, upgraded phones and then failed an automated liveness check during KYC re-verification. Simultaneously a thinly traded spot token she held was delisted this week. The combination created a multi-domain recovery problem: locked CEX access, potential withdrawal freezes pending manual review, and the need to recover or migrate a self-custodial Web3 holding. We’ll use this scenario to unpack how OKX’s account model, verification process, custody architecture, and platform features interact — and what a trader should do differently next time.
How OKX structures access and why each layer matters
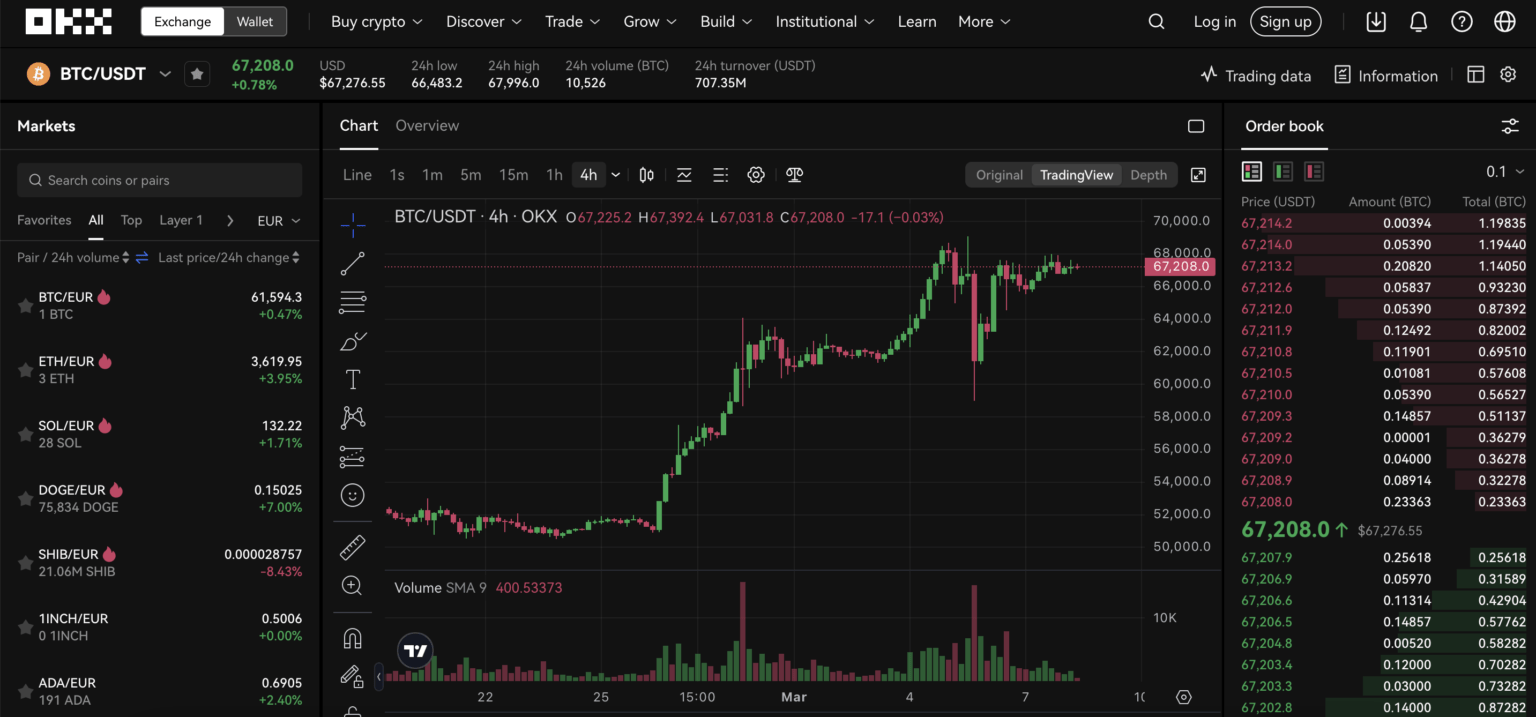
Mechanism first: OKX combines a centralized exchange (CEX) with a non-custodial Web3 wallet and DEX aggregator. That means you interact across three primary surfaces: the account login to the centralized order books, the Web3 wallet that holds private keys, and the cross-chain bridges/Dex routes that move tokens between chains. Each surface has different security guarantees and failure modes. The CEX protects assets on deposit with cold-storage multi-signature systems (OKX reports keeping over 95% of assets offline), whereas the Web3 wallet hands you custody responsibility via a seed phrase. Understanding which asset lives where — exchange custody versus your seed — is the single most important practical mental model.
Trade-off: central custody reduces your individual operational burden (no seed to lose) and gives you access to margin, futures, and centralized order books (including up to 125x leverage on selected derivatives). The cost is counterparty dependence: withdrawals are subject to exchange procedures, delisting policies, and KYC checks. Self-custody eliminates counterparty risk but shifts responsibility — and catastrophic loss becomes possible if seed phrase or hardware wallet is mishandled.
Verification (KYC) mechanics and the operational risks U.S. traders should know
OKX requires Know Your Customer (KYC) verification: government-issued ID and a facial liveness check. Mechanically, the liveness check is an AI-driven step intended to confirm the person matches the ID. In many practical cases the automated step clears, but failures can trigger manual review, slowing account reactivation or withdrawals. In the Sarah scenario, a phone upgrade altered camera characteristics and the automated check flagged the submission. The result is not a security failure by design, but an operational bottleneck: during review, margin positions may be restricted and delisted asset handling becomes time-sensitive.
Limitation and boundary condition: KYC processes are necessary to comply with AML rules; they are also imperfect. Automated facial-recognition tools have false negatives and can be sensitive to lighting, hardware differences, or cosmetic changes. For U.S. traders, the implication is procedural: keep an archival copy of the ID used for initial KYC, follow provider photo guidelines exactly, and expect intermittent manual review if anything about your device or appearance changes. Treat account verification not as a one-time box to tick but as an ongoing operational dependency.
Security architecture: what OKX defends and what you must defend
Mechanism: OKX uses military-grade encryption, AI-driven detection for suspicious logins, mandatory two-factor authentication (2FA), and cold storage with multi-signature for most assets. That combination materially reduces large-scale exchange hacks. However, the remaining attack surfaces are account credential compromise, social engineering during KYC recovery, and phishing aimed at capturing Web3 seed phrases. In Sarah’s case, the urgent pressure to regain access after a delisting created a social-engineering risk — attackers frequently target users experiencing recovery pain with fake support pages and credential prompts.
Practical framework: defend along three vectors — authentication hygiene (strong unique password + hardware 2FA where possible), procedural resilience (backup of KYC documents and recovery contacts), and custody segmentation (keep only trade capital on exchange; move longer-term holdings to a self-custodial wallet or hardware wallet). This last measure trades convenience for safety: moving assets off-exchange removes leverage and instant margin capability but reduces counterparty and regulatory friction during account incidents.
Delisting: why routine market maintenance can escalate into operational disruption
Delistings are routine — this week OKX removed several low-volume spot pairs. Mechanically, exchanges delist assets for liquidity, compliance, or market quality reasons. For traders holding thinly traded tokens, delisting creates a narrow window: the asset may be moved to a withdrawal-only mode or require trading in a reduced market before full removal. If the trader’s account is under verification review or withdrawals are temporarily disabled, the asset’s liquidity could evaporate and the only recourse is off-exchange recovery through seed-controlled wallets.
Decision-useful insight: always map which of your positions are on-exchange custody versus in your Web3 wallet. If you hold low-liquidity tokens on-exchange, set an alert for delisting announcements and prioritize exits or withdrawals ahead of removal. For U.S. traders, adjust position sizing in low-volume tokens to account for the possibility that operational delays (KYC review, security holds) could make timely exits impossible.
For more information, visit okx login.
Practical checklist: logging in, verifying, and recovering access — a trader’s playbook
Here is a reusable sequence that synthesizes the earlier mechanisms into practice. First, separate custody by purpose: on-exchange for active margin and derivatives; self-custodial for long-term holdings. Second, operationalize KYC: store a secure copy of the ID you used, keep a notarized backup if you rely on manual re-verification often, and use a stable device for liveness checks. Third, harden authentication: prefer hardware 2FA (security keys) where supported, enable biometrics only for convenience on personal devices, and register multiple 2FA methods, not just SMS. Fourth, prepare for delisting: maintain an alert feed for token-pair updates and avoid holding large positions in thin markets on exchange custody. For step-by-step login help many traders find a curated guide useful; for an OKX-specific walkthrough see this okx login resource.
Trade-offs: each mitigation costs time or convenience. Hardware 2FA incurs a small purchase and the risk of physical loss; cold storage reduces trading agility. Your decision should be driven by a simple matrix: asset risk (size × illiquidity) versus required access speed (how quickly you might need to move the asset). High-value, low-liquidity holdings justify extra custody friction; short-term margin positions require fast exchange access but carry greater counterparty dependence.
Where the system still breaks: unresolved issues and what to watch
There are three open pressure points to monitor. First, automated KYC liveness accuracy: regulators push for robust identity checks, but current systems can be brittle across devices and demographics. Second, regulatory change: U.S. policy shifts around stablecoin rules or derivatives restrictions could change access patterns or leverage availability. Third, cross-chain bridge risk: the OKX DEX aggregator simplifies swaps across chains but relies on external liquidity and smart contracts that can be exploited. These are not hypothetical — all three are plausible nodes of failure that have real operational consequences for traders.
Signals to watch: changes in OKX’s Proof of Reserves disclosures, updates to KYC flow or required documents, announcements about delisted pairs, and any incidents involving third-party bridges. If you see repeated manual KYC reviews or an uptick in delistings for regulatory reasons, reduce reliance on on-exchange custody for any asset you cannot afford to be stuck on the platform.
FAQ
Q: If my KYC fails during a liveness check, what immediate steps should I take?
A: Stop and document what you submitted. Take a fresh ID photo under recommended lighting and retake the liveness check on a stable device (avoid VPNs or unusual network routes). Prepare a secondary verification path (support ticket with embedded ID scans) and enable account-wide measures that reduce urgency, such as moving non-essential assets to an external wallet beforehand. Expect manual review to take time; plan positions accordingly.
Q: Should I use OKX’s non-custodial wallet or keep everything on the exchange?
A: Use both, with clear roles. Keep active trading capital and margin collateral on OKX for liquidity and derivative access. Place long-term holdings and illiquid tokens in the non-custodial wallet or hardware wallet where you control the seed. This hybrid approach balances convenience and security. Remember: self-custody shifts full responsibility for seed safety to you.
Q: How do delistings affect margin and futures positions?
A: Delistings typically concern spot pairs; margin and futures are governed by separate product rules and can be closed automatically if underlying liquidity collapses. If a spot pair is delisted and you hold a cross-margin or hedged position involving that token, contact support and consider closing or reducing exposure immediately, because automated liquidation triggers may follow if the market becomes illiquid.
Q: What are practical signs of a phishing attempt aimed at account recovery?
A: Look for unsolicited messages asking for KYC re-submission through non-official channels, URLs that mimic but do not exactly match official domains, and requests for seed phrases or full 2FA codes. Official support will never ask for your seed phrase. When in doubt, open support from the exchange website or app and avoid following links in messages.
Takeaway: logging into OKX is a compound operational problem, not a single credential check. For U.S. traders the practical framework is simple: classify assets by custody and liquidity, harden authentication and KYC readiness, and adopt a recovery-first mindset that anticipates device changes and delisting windows. Do these, and you convert a recurring annoyance into a manageable procedure — and avoid the scenario where a routine device upgrade becomes a forced liquidation or permanent loss.
